The Advent of Brain Chips and Body Chips: Exploring Relevance to Biblical Prophecy
The idea of implantable chips in the human body once seemed like a distant fantasy. However, as technology advances at an unprecedented pace, this concept is rapidly becoming a reality. Brain chips and body chips, once confined to the pages of speculative literature, are now on the brink of integration into our daily lives. But as we marvel at the potential benefits of such technology, it’s crucial to consider its implications, not only from a scientific and ethical standpoint but also in the context of ancient prophecies, particularly those found in the Bible concerning the Mark of the Beast.
Brain Chips: Enhancing Human Capability
Brain chips, also known as neural implants or brain-computer interfaces (BCIs), are devices that connect directly to the brain to augment its functionality. These implants hold the promise of restoring lost sensory functions, enhancing cognitive abilities, and even enabling direct communication between individuals and machines. For people with disabilities, such technology offers newfound independence and quality of life. Researchers are also exploring the potential of brain chips in treating neurological disorders such as Parkinson’s disease and epilepsy.
Body Chips: Monitoring Health and Identity
On the other hand, body chips, often referred to as RFID (Radio-Frequency Identification) implants or subdermal implants, are small devices inserted under the skin. They serve various purposes, from tracking inventory in warehouses to unlocking doors with a wave of the hand. In terms of healthcare, body chips hold the potential to revolutionize patient care by continuously monitoring vital signs and transmitting data to healthcare providers in real time. Moreover, proponents argue that these implants could streamline identification processes, enhancing security and convenience in everyday transactions.
Biblical Relevance: The Mark of the Beast
The concept of implantable chips in the human body inevitably evokes parallels with biblical prophecy, particularly the notion of the Mark of the Beast as described in the book of Revelation. According to Revelation 13:16-18, those who refuse to receive the mark on their right hands or foreheads will be unable to buy or sell:
“And he causeth all, both small and great, rich and poor, free and bond, to receive a mark in their right hand, or in their foreheads: And that no man might buy or sell, save he that had the mark, or the name of the beast, or the number of his name. Here is wisdom. Let him that hath understanding count the number of the beast: for it is the number of a man; and his number is Six hundred threescore and six.”
While interpretations of this passage vary widely, some believers view the development of implantable chips as a potential precursor to the fulfillment of this prophecy. They caution against the widespread adoption of such technology, warning of its potential to be co-opted for nefarious purposes and its role in a future system of control and surveillance.
Ethical Considerations and Societal Implications
Regardless of one’s religious beliefs, the advent of brain chips and body chips raises profound ethical questions and societal implications. Concerns about privacy, consent, autonomy, and inequality abound. Who will have access to this technology, and who will be left behind? How will data collected by these implants be used, and by whom? Will individuals be coerced into receiving implants for the sake of societal conformity or economic participation?
As we navigate this brave new world of implantable technology, it is imperative to tread cautiously, guided by ethical principles and a commitment to safeguarding human dignity and rights. While the potential benefits of brain chips and body chips are undeniable, we must remain vigilant against their misuse and unintended consequences.
The emergence of brain chips and body chips represents a remarkable leap forward in human technological advancement. However, it also prompts us to reflect on our responsibilities as stewards of innovation and guardians of our shared humanity. As we embrace the promise of progress, let us do so with humility, wisdom, and a steadfast commitment to the values that define us as moral beings.
DWP Bank Checks: Streamlining Financial Transactions
Financial transactions, efficiency, security, and reliability stand as pillars upon which trust is built. DWP Bank Checks, an innovative solution in the domain of banking, epitomizes these attributes, offering a streamlined approach to traditional check processing. As digital transformation continues to reshape the landscape of banking and finance, DWP Bank Checks emerge as a contemporary tool, blending the convenience of digital processes with the familiarity and assurance of paper-based transactions.
Evolution of Checks in the Digital Era
Checks have long been a staple of financial transactions, offering a tangible medium for transferring funds between parties. However, the advent of digital technologies has spurred significant advancements in payment systems, leading many to question the relevance of traditional paper checks. Despite this, checks have endured, evolving to meet the demands of the digital age.
DWP Bank Checks represent a convergence of traditional check payments with modern digital infrastructure. Developed by leading financial institutions in collaboration with technological innovators, these checks leverage digital workflows to enhance efficiency, security, and convenience.
Understanding DWP Bank Checks
DWP Bank Checks, also known as Digital Wallet Protocol Bank Checks, introduces a novel approach to check issuance, processing, and clearance. At its core, the concept revolves around digitizing the entire lifecycle of a check, from creation to settlement. Unlike traditional paper checks, DWP Bank Checks harness the power of blockchain technology and secure digital signatures to authenticate transactions, ensuring integrity and preventing fraud.
Key Features and Benefits
- Instant Settlement: By digitizing the check issuance process, DWP Bank Checks enables near-instantaneous settlement, eliminating the delays associated with traditional check-clearing processes. This rapid settlement accelerates cash flow and enhances liquidity for businesses and individuals alike.
- Enhanced Security: Leveraging cryptographic techniques and blockchain technology, DWP Bank Checks offers robust security measures to safeguard against unauthorized tampering or counterfeiting. Each transaction is cryptographically signed, creating an immutable record of ownership and authenticity.
- Cost Efficiency: Traditional check processing incurs various costs, including printing, transportation, and manual processing. DWP Bank Checks significantly reduce these overheads by digitizing the entire workflow, resulting in cost savings for both banks and customers.
- Accessibility and Convenience: Digitalization ensures accessibility to banking services anytime, anywhere. DWP Bank Checks can be issued, deposited, and cleared through online platforms or mobile applications, providing unparalleled convenience to users.
Implementation and Adoption
The adoption of DWP Bank Checks requires collaboration between financial institutions, regulatory bodies, and technology providers. Key steps in implementing DWP Bank Checks include:
- Technology Integration: Banks and financial institutions integrate DWP protocols into their existing systems, enabling seamless interoperability with digital wallets and payment networks.
- Regulatory Compliance: Regulatory frameworks must adapt to accommodate the nuances of digital check payments, ensuring compliance with anti-money laundering (AML) and know-your-customer (KYC) regulations.
- User Education: Educating customers about the benefits and usage of DWP Bank Checks is crucial for driving adoption. Clear communication regarding security measures and transaction processes fosters trust and confidence among users.
Future Outlook
The emergence of DWP Bank Checks signals a paradigm shift in the way traditional banking instruments are perceived and utilized in the digital age. As technology continues to evolve, we can expect further refinements and innovations in digital payment systems, offering unparalleled efficiency, security, and convenience to users worldwide.
DWP Bank Checks represent a fusion of tradition and innovation, offering a compelling solution for modernizing check payments in an increasingly digital world. By embracing digitalization, financial institutions can unlock new possibilities for enhancing customer experiences and driving operational excellence in the realm of banking and finance.
The connection between the Department for Work and Pensions (DWP) and chip implants lies in the potential for utilizing advanced technology to combat fraud and ensure the integrity of social welfare programs. In the future, chip implants could be employed as a means of securely and accurately verifying individuals’ identities, eligibility, and entitlements within the DWP system. By integrating biometric data and personal information directly into the chips, authorities could monitor transactions and activities in real-time, detecting any discrepancies or instances of fraud with unprecedented precision. This could lead to a more efficient and transparent welfare system, where resources are allocated more effectively, and instances of misuse or exploitation are significantly reduced. However, ethical considerations regarding privacy, consent, and potential misuse of such technology must be carefully addressed to ensure that the benefits of chip implants in combating fraud do not come at the expense of individual rights and freedoms.
Debunking Dystopian Visions: The Reality of Chip Implants in the Future
In popular culture and speculative fiction, the notion of a dystopian future where individuals are universally chipped, either with brain chips or body chips, has often been a recurring theme. However, while the concept may fuel the imaginations of writers and filmmakers, the reality of such a scenario is far more nuanced. Rather than succumbing to dystopian fears, a careful examination reveals a future where chip implants, if implemented, would likely coexist with ethical guidelines, regulations, and individual choice, ultimately shaping a future that is more nuanced than dystopian narratives suggest.
The Promise and Perils of Chip Implants
Chip implants, whether embedded in the brain or the body, hold the potential to revolutionize various aspects of human life. From enhancing cognitive abilities and memory to providing seamless access to information and services, the applications are vast. Additionally, body chips could offer medical benefits, such as continuous health monitoring and real-time disease detection, improving healthcare outcomes.
However, alongside these promises come legitimate concerns about privacy, autonomy, and the potential for misuse. The idea of a ubiquitous surveillance state, where individuals are constantly monitored and controlled through their implants, is a valid apprehension. Furthermore, questions regarding data security and the risk of hacking raise significant ethical dilemmas.
The Importance of Ethical Considerations
In envisioning the future of chip implants, it is essential to prioritize ethical considerations and establish clear guidelines to safeguard individual rights and autonomy. Robust privacy protections, stringent regulations on data collection and usage, and transparent governance structures are imperative to prevent abuses of power and ensure accountability.
Moreover, the principle of informed consent should underpin any implementation of chip implants. Individuals must have the freedom to choose whether to undergo implantation and maintain control over their personal data. Any coercion or imposition would undermine the ethical foundation of such technologies.
The Role of Regulation and Oversight
Regulatory frameworks play a pivotal role in shaping the future of chip implants. Government agencies, in collaboration with experts from various fields, must develop comprehensive regulations that balance innovation with ethical considerations. This includes establishing standards for data security, enforcing privacy laws, and conducting regular audits to assess compliance.
Furthermore, international cooperation is crucial to address the global implications of chip implantation. Harmonizing regulations across borders and fostering dialogue among nations can help mitigate potential disparities in implementation and ensure universal adherence to ethical standards.
Individual Choice and Empowerment
Ultimately, the future of chip implants hinges on individual choice and empowerment. While some may choose to embrace the benefits of implantation for medical, cognitive, or convenience purposes, others may opt to forego such enhancements, preferring to maintain their natural state. Respecting diverse perspectives and values is essential in fostering a future where technological advancements serve to empower rather than oppress.
Dystopian Nightmare: The Consequences of Mass Brain and Body Chip Implantation
Where technology blurs the lines between humanity and machinery, the prospect of brain and body chip implantation has sparked intense debate and fear. While proponents tout the benefits of enhanced connectivity and convenience, the potential consequences of widespread chip implantation present a chilling worst-case scenario.
Imagine a society where individuals willingly submit to the insertion of microchips into their brains and bodies. At first, it seems innocuous—an easy way to streamline daily tasks and stay connected in an increasingly digital world. However, as the technology becomes ubiquitous, its insidious effects begin to surface.
Censorship reigns supreme as those in power gain unprecedented control over the flow of information. With access to individuals’ thoughts and actions through brain chips, dissenting voices are swiftly silenced. Any hint of rebellion is swiftly quashed, and freedom of expression becomes a relic of the past.
The ability to buy, sell, and trade is no longer a matter of personal choice but is dictated by the whims of the ruling elite. Financial transactions are seamlessly conducted through body chips, but with this convenience comes a loss of autonomy. Those who refuse to comply with the system find themselves ostracized, unable to participate in society’s basic functions.
Every movement is monitored, every action scrutinized. Privacy becomes a distant memory as individuals live under constant surveillance. The illusion of freedom is shattered as personal autonomy is sacrificed in the name of security and efficiency.
In this dystopian reality, humanity becomes enslaved to technology, stripped of its inherent dignity and worth. The line between man and machine blurs until it is no longer discernible. The consequences of mass chip implantation are far-reaching and irreversible, leading to a society devoid of humanity’s most fundamental traits—compassion, empathy, and free will.
As we contemplate the potential pitfalls of advancing technology, it is essential to heed the warnings of history and literature. Biblical references to the “mark of the beast” serve as a cautionary tale, reminding us of the dangers of allowing technology to usurp our humanity. The mark, often interpreted as a symbol of subservience to a tyrannical regime, serves as a stark reminder of the perils of relinquishing control to external forces.
The prospect of brain and body chip implantation presents a chilling worst-case scenario, where censorship, control, and surveillance run rampant. As we navigate the complexities of an increasingly digital world, we must proceed with caution, lest we sacrifice our humanity on the altar of technological progress. The consequences of such a fate are too dire to ignore, reminding us that the true mark of humanity lies not in our technological prowess, but in our ability to uphold our values and preserve our autonomy.
Conclusion: A Nuanced Future
The idea of a dystopian future characterized by universal chip implantation oversimplifies the complexities of technological progress and human society. While chip implants hold tremendous potential to transform various aspects of our lives, their implementation must be guided by ethical considerations, robust regulations, and respect for individual autonomy. By embracing these principles, we can shape a future that is not dystopian, but rather diverse, equitable, and empowered.
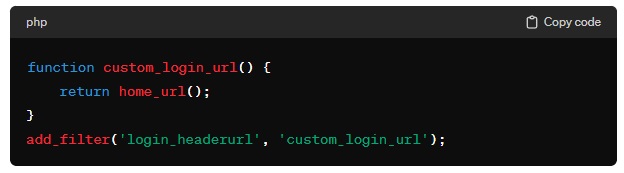
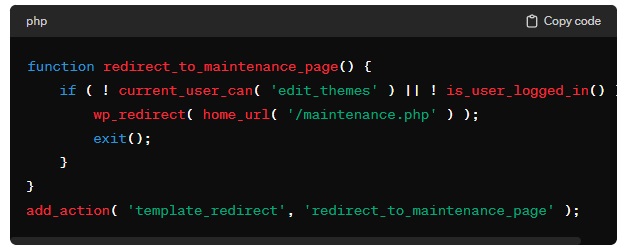
In the face of censorship, iRenata’s experience serves as a poignant reminder of the ongoing struggle for freedom of expression in the digital age. Despite attempts to silence dissenting voices, individuals like iRenata refuse to be stifled, demonstrating resilience and resourcefulness in circumventing censorship.
iRenata’s decision to publish her thoughts on her own platform, linking back to the original article, exemplifies the power of alternative avenues for communication in an era where traditional channels may be restricted or controlled. By leveraging the internet and social media, individuals can bypass censorship and reach audiences directly, ensuring that diverse perspectives continue to be heard.
Regarding DWP bank checks, while their functionality may not represent a revolutionary breakthrough in accessing bank accounts, their significance lies in their potential to streamline financial transactions and enhance efficiency. While traditional banks have long provided access to accounts, the emergence of challenger banks highlights the evolving landscape of financial services, offering consumers new options and disrupting established norms.
Ultimately, the challenges posed by censorship and the evolution of banking technology underscore the importance of vigilance in safeguarding freedom of expression and promoting innovation. In an increasingly interconnected world, the ability to exchange ideas freely and access financial services without unnecessary barriers is essential for fostering progress and ensuring inclusivity. As we navigate these complexities, it is imperative to uphold principles of transparency, accountability, and respect for individual rights, ensuring that advancements in technology and finance serve the greater good of society.
**This is the article iRenata was censored, where she attempted to comment “everyone will be implanted with chips in the future”. DWP bank checks timetable revealed – when new crackdown will start (msn.com)
Endnote: If you are interested in acquiring the domains www.brainchip.uk and www.brainchips.uk for your business or project, please feel free to contact iRenata using the online form available on their website. These domains could serve as valuable assets in the field of technology, innovation, or any related ventures. Don’t hesitate to reach out to secure these domain names and explore the possibilities they may offer for your endeavors.
Further Reading
- https://ukdomainbrokers.ukwebsitedesigners.co.uk/brain-chips-domain-names-for-sale
- https://disabledentrepreneur.uk/rewiring-our-brains-tdcs
- https://disabledentrepreneur.uk/the-subconscious-mind-quantum-jumping
#brainchip #brainchips #chipimplants #neurology #bcis #neuralimplants #braincomputerinterfaces #markofthebeast #bible #dwpbankmonitoring